System Center Endpoint Protection & Config Manger in Citrix Xenapp/PVS
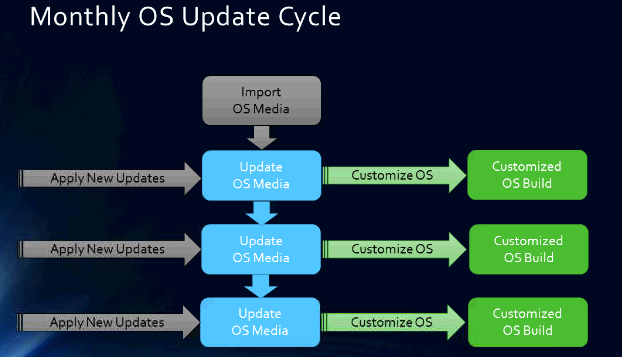
One o f my clients is undergoing a complete Datacenter transformation. With this comes a lengthy list of multiple decisions on what to bring over from the old to the new. This post will focus on transitioning their current virtual machine anti-virus protection to a new solution. The new solution is System Center Configuration Manager/Endpoint Protection in a Citrix XenApp/PVS environment. This consists of Citrix Xenapp 6.5, PVS 7.1, and System Center 2012 R2. Although, I don’t really see any reason these same steps wouldn’t work in later versions of Xenapp and PVS.
f my clients is undergoing a complete Datacenter transformation. With this comes a lengthy list of multiple decisions on what to bring over from the old to the new. This post will focus on transitioning their current virtual machine anti-virus protection to a new solution. The new solution is System Center Configuration Manager/Endpoint Protection in a Citrix XenApp/PVS environment. This consists of Citrix Xenapp 6.5, PVS 7.1, and System Center 2012 R2. Although, I don’t really see any reason these same steps wouldn’t work in later versions of Xenapp and PVS.
Currently they are using Trend Micro Deep Security 9.5 and OfficeScan 11.x to protect their Endpoints as well as their virtual machines. I have to say, I do really like Deep Security to protect the virtual machines. Very little maintenance is required and it just seems to do its job well. Unfortunately, somebody has to pay the bills to keep it licensed. The client decided to utilize their current Microsoft ‘Enterprise Agreement’ licensing and protect themselves with System Center Endpoint Protection, with Config Manager managing the agents.
While I do realize there are other blog posts out there that contain similar information on this topic, I was not able to use just one site to complete this project. At the bottom of the post I document where I got most of the resources used to complete this project.
First, we need to install SCCM into the image. SCCM is used to manage and control the agents centrally. It is used to control all the special exclusions, real-time scan settings, etc… Without it, you would have to manage each agent manually.
SCCM Steps:
- Create a new PVS Version
- Install the ConfigMgr client
a. Launch the SCCM setup client from the SCCM server – \\SCCMserver\Client\CCMSetup.exe
b. Add ‘domain\username’ domain account as local admin on the xenapp 6.5 server.
SCEP Steps:
- Run bat file:
- MKDIR e:\SCEP
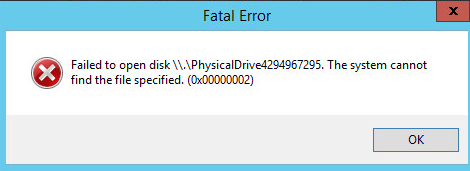
- this is the ‘cache drive’ used to store RAM overflow, event viewer, pagefile, and SCEP anti-virus definitions.
- cmd.exe /c Mklink /d /j “C:\ProgramData\Microsoft\Microsoft Antimalware” E:\SCEP
- Install SCEP executable
\\servername\Client\SCEPinstall.exe
- MKDIR e:\SCEP
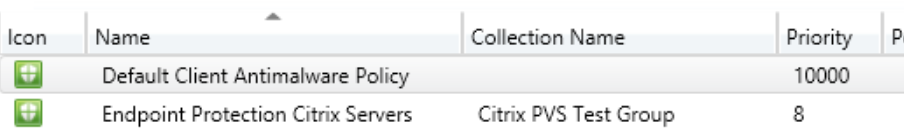
- In SCCM After SCEP/SCCM is deployed:
Final Steps:
- Seal Image using the following bat file:
- Net stop “SMS Agent Host”
- del %WINDIR%\smscfg.ini
- Powershell -command “Remove-Item -Path HKLM:\Software\Microsoft\SystemCertificates\SMS\Certificates\* -Force”
- wmic /namespace:\\root\ccm\invagt path inventoryActionStatus where InventoryActionID=”{00000000-0000-0000-0000-000000000001}” DELETE /NOINTERACTIVE
- Del “c:\programdata\citrix\pvsagent\LocallyPersistedData\CCMData\CCMCFG.bak”
- Use Xenapp Role Manager to do the final seal and shutdown the image.
Confirm Steps:
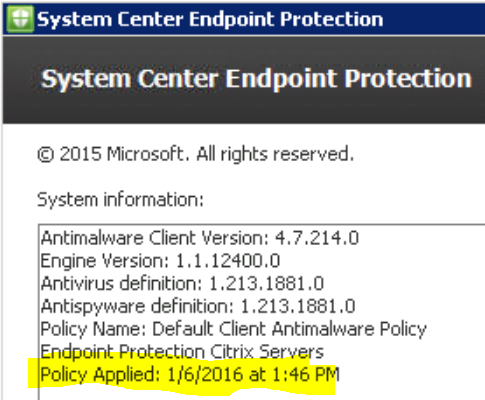
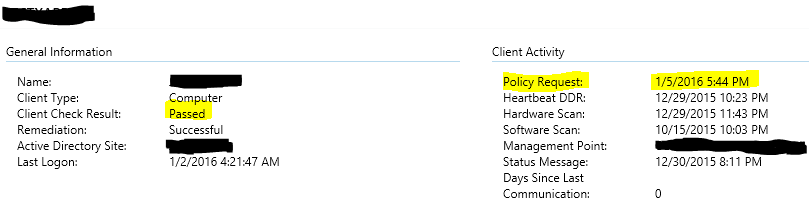
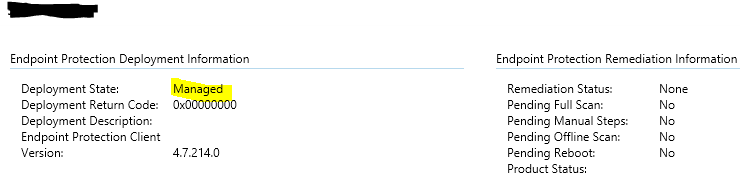
- Confirm SCCM Policy Deployment to the SCEP agent (on the SCEP agent, drop down arrow, about)
- Confirm the devices are manageable in SCCM
- Test Protection
- I was able to test protection using a ‘dummy’ anti-virus test file
- http://www.eicar.org/
- create the .txt file with the string in it.
- Safe the file
- SCEP should recognize it as a threat and clean the file appropriately
That’s it, your Citrix PVS machines should now be protected by System Center Configuration Manager and System Center Endpoint Protection. Now I realize there are 100 ways to skin a cat. Please let me know if have/find any efficiency’s in the steps and i’ll be happy to change the contents of the site.
A big THANK YOU to everyone involved in creating and helping answer questions on the following sites:
SCCM:
- http://henkhoogendoorn.blogspot.com/2013/07/prepare-configmgr-client-for-sysprep-or.html
- http://social.technet.microsoft.com/wiki/contents/articles/23923.implementing-sccm-in-a-xendesktop-vdi-environment.aspx
- http://scug.be/sccm/2013/03/27/citrix-provisioning-services-and-microsoft-system-center-configuration-manager-2012-sp1/
- http://nielsvdijk.blogspot.com/2014/01/ConfigMgrCitrixIdentityStore.html
- http://discussions.citrix.com/topic/330321-pvs-vdisk-getting-duplicate-guids-for-sccm-client/
SCEP:
- http://www.kylewise.net/citrix/xendesktop/system-center-endpoint-protection-with-xendesktop/
- http://mshorrosh.blogspot.com/2014/06/implementing-scep-2012-on-citrix-pvs-vdi.html
- https://social.technet.microsoft.com/Forums/en-US/3a8bbedf-3eff-484d-aa2d-85940f5eb040/forum-faq-how-to-move-microsoft-antimalware-folder-of-a-scep-client-to-another-drive-in-task?forum=configmanagergeneral
- https://www.windows-noob.com/forums/topic/6106-using-system-center-2012-configuration-manager-part-6-adding-the-endpoint-protection-role-configure-alerts-and-custom-antimalware-policies/

How do you handle the problem, with new PVS targets?
If they have “E:\SCEP” fresh without any data?
And why do you delete c:\programdata\citrix\pvsagent\LocallyPersistedData\CCMData\CCMCFG.bak?
What is stored in it?
And I get no access to c:\programdata\citrix\pvsagent\LocallyPersistedData…
If it’s a new target, simply create a new folder (SCEP) on the write cache driver. It can be any letter. Then run through the bat file.
I got no access to that file as well, you have to take ownership of the directory, then you can delete the file. The file contains static information about the target, however upon reboot, the information changes, which creates multiple entries for the same target. Hope this helps.